This is our third piece in a series on email deliverability and the features that affect it. To catch up, check out our first and second pieces.
The world of email marketing is always changing. Email services are always looking for ways to better their user experience, or add an extra layer of security. And email marketers always need to be ready to adapt.
When Google announced that they will support BIMI, a new feature coming onto the market that offers both enhanced user experience and added security, marketers began asking — Is this the next big thing?
The answer? Maybe!
As with any new feature in the email marketing landscape, it’s time to investigate. Let’s take a look at what, exactly, BIMI is, how it works, and how you can implement it in your email marketing strategy.
What is BIMI?
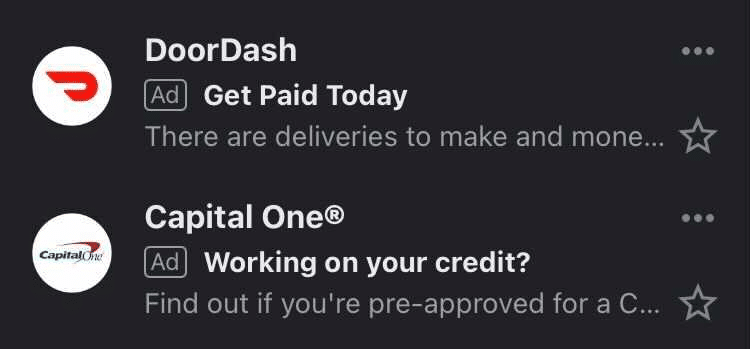
BIMI stands for Brand Indicators for Message Identification. In short, BIMI shows your company’s logo next to the marketing emails you send while they’re in your subscribers’ inboxes, like the photo below.
BIMI serves a couple of unique purposes. First, it brings brand recognition to the sender’s emails by placing the logo next to them. This creates a strong visual association.
Second, BIMI works like a security feature. With your logo displaying next to your message, this validates to your subscribers that this message is, indeed, from you, not an imposter.
In a time when it’s harder to stand out in an inbox than ever before, and in a day when phishing emails are on the rise, you can see why this would be a very appealing feature to email marketers. You get brand recognition in the inbox, more protection over your brand reputation, and better control over your subscribers’ experience.
Win, win, win — right?
How do you implement BIMI?
This is where that maybe comes in.
While the technical elements used to pull the logo is the same across mailbox providers, the requirements for BIMI vary between them.
Verizon Media Group (Yahoo, AOL, etc.) currently requires the following:
- Logo validation
- DMARC-level authentication on the domain’s DNS
- A healthy sender reputation
Google requires the same for Gmail, along with a few more things like a logo copyright and a VMC (Verified Mark Certificate). This makes BIMI implementation at Google more than just a technical adjustment, as getting those elements in place can be a long process.
To get BIMI to work for Gmail, you’ll have to go through the following requirements:
- Set up DKIM authentication with your domain for your mail streams
- Set up a DMARC record with a policy other than p=none
- Copyright your logo
- Purchase a VMC for that logo
- Create an SVG Tiny PS version of your official logo
- Set up a BIMI TXT record on your domain’s DNS
- Test your setup to see if it functions properly
And after all that, your logo can appear in the inbox next to your emails in a Gmail inbox.
What does BIMI mean for me?
The ability to provide email validation and greater brand visibility in the inbox is an appealing thing for marketers.
So how do you know if it’s a right fit for you?
- Look at a breakdown of your subscribers’ email client usage and see if these listed BIMI-supporters are well represented there.
- Look at the requirements for each provider and see which ones you already have in place.
- Look at what it would require to set up the remaining elements. Note: make sure to consider BIMI-setup-assistance services if that will help you get started.
And remember — because the requirements are currently on a per email-provider basis, the decision to implement doesn’t have to be all or nothing.
If you’ve determined you’d like to start, you can begin by meeting Yahoo’s requirements and testing with those users. Then, if you’re seeing positive results, that might be a sign to invest in the setup required to use BIMI for Gmail users as well.
Wrap Up
Email security and validation have never been more needed in the history of email — and BIMI is a great chance to provide both of those things.
Whether you are planning to move forward with this or not, it is important to remember that new technological elements work best when paired with quality list maintenance.
If BIMI sounds like a great fit for you and your organization, then implementing is a no-brainer. Getting the proper authentications and copyrights can be time-consuming if not already in place. But, for a more secure and more trusted user experience, it could be well worth it.